ICAN TCI

ICAN
ICAN Technology Competence Initiative (TCI) is a program of the Institute of Chartered Accountants of Nigeria aimed at making Chartered Accountants technologically compliant.
Its objective is to promote computer literacy consistent with Information and Communication adoptions in organization for Chartered Accountants.
TCI is a prerequisite for the induction of new members as stipulated by ICAN.
CRISC

CRISC
Certified in Risk and Information Systems Control (CRISC) is a certification for information technology professionals with experience in managing IT risks, awarded by ISACA. To gain this certification, candidates must pass a written examination and have at least eight years of information technology or business experience, with a minimum of three years work experience in at least three CRISC domains.
The intent of the certification is to provide a common body of knowledge for information technology/systems risk management, and to recognize the knowledge of enterprise and IT risk that a wide range of IT and Business practitioners have acquired, as well as the capability to: design, implement and maintain information system (IS) controls, to mitigate IS/IT risks.
The CRISC requires demonstrated knowledge in five functional areas or ‘domains’ of IT risk management:
- Risk identification, assessment and evaluation
- Risk response
- Risk monitoring
- Information systems control, design and implementation
- IS control, monitoring and maintenance
CISM

CISM
Certified Information Security Manager (CISM) is a certification for information security managers awarded by ISACA (formerly the Information Systems Audit and Control Association). To gain the certifications, individuals must pass a written examination and have at least five years of information security experience with a minimum three years of information security management work experience in particular fields.
The intent of the certification is to provide a common body of knowledge for information security management. The CISM focuses on information risk management as the basis of information security. It also includes material on broader issues such as how to govern information security as well as on practical issues such as developing and managing an information security program and managing incidents.
The point of view in the certification is that of widely accepted cross-industry best practices, where information security gets its justification from business needs. The implementation includes information security as an autonomous function inside wider corporate governance.
CISA

CISA
Certified Information Systems Auditor (CISA) is a globally recognized certification in the field of audit, control and security of information systems. CISA gained worldwide acceptance having uniform certification criteria, the certification a high degree of visibility and recognition in the fields of IT security, IT audit, IT risk management and governance. Vacancies in the areas of IT security management, IT audit or IT risk management often ask for a CISA certification. The certification is challenging and is associated with a high failure rate. CISA is awarded by the Information Systems Audit and Control Association (ISACA)
Computer Network Solution
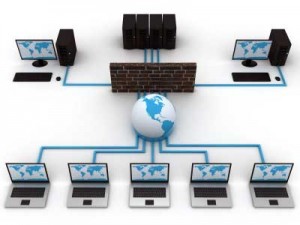
Computer Network
Overview
- For Organisations to have an effective Enterprise-Network solution, the infrastructure has to be at a level of support such that minimum downtime is experienced by the organisation.
- High-speed networks are built with devices such as Core and Edge Switches, Routers, Radios, etc, the continued availability of your network resources is a function of the state of health of these components and devices. A failure of a router could lead to disastrous situations hence both on-site and off-site support become crucial for organisations to experience optimum performance from their network solutions.
Main Objectives
- Our main focus in this type of engagement is to provide component and device level training and support for Organizations, whilst your local Engineers will be trained to provide levels 1 and 2 support. This could be by phone or internet service routines where off- site is the case.
- In a similar vein, the on-site support runs at three levels; where on-site engineers try to resolve problems, unable to do so, they can escalate it to the second and third levels of support respectively
Core capacity building issues for Engineers include:
- Proper operation of general computer systems, including: PCs, thin client terminals, printers, fax machines, UPSs, stabilisers, etc.)
- Systems Maintenance & 1st Level troubleshooting of general computer systems
- Server hardware configuration
- Remote server management, using OEMmanagement tools
- UPS-driven shut-down of servers
- Fundamentals of LANs & WANs, structuredcabling (UTP, & power), data switches, andbroadband wireless infrastructures
- Maintenance & 1st Level troubleshooting of the installed structured cabling infrastructures and data switches.
- Fundamentals of routers and network routing
- Fundamentals of voice-over-IP technologies
- Fundamentals of network security, (incl. firewall& VPN technologies)
- Maintenance & 1st Level troubleshooting of thesecurity and voice/IP-enabled gateway routersat the LG/LCDAs/SA’s ICT Centres
- Written Exam – of all the above subjects
- Practical Exam – Hands-on use &troubleshooting of the equipment
Incident Response/ Prevention and Computer Hacking and Investigation

Computer Hacking Prevention
Overview
- Incident Response is a generalised term that refers to the immediate response by a person or an organization to an attack.
- This can be from an internal employee or via malicious external sources to include crackers and/or terrorists. An organised and careful reaction to an incident can mean the difference between complete recovery and total disaster.
- When an incident has occurred or is detected, the forensic investigation processes used are vital. Correct procedures ensure that evidence remains sound when being located and extracted from applicable devices and media.
- Approaches may range from the use of simple data recovery and disk mirroring tools to complex techniques such as the application of reverse engineering to enable the investigator reconstruct the evidence needed to prosecute the offender.
Main Objectives
- When computer systems security has been breached and the evidence source destroyed, our forensic investigators will assist in:
- Locating and retrieving electronic evidence from many devices which include:
- Servers/ Desktops/Laptop
- Zip Drives/ Back-up Tapes
- USB devices
- PDA’s/Mobile Phones
- Digital Cameras
- Network Traffic
- E- Mails Communications
- Forensic report is generally raised to be used to prosecute the offender
- Locating and retrieving electronic evidence from many devices which include:
- Conducting an investigation under a properly controlled environment
- Generating forensic evidence that is tenable in any court of law
- Generating forensic investigation report based on all material evidence that will help control the crime.
Corporate Fraud Audit and Forensic Investigation
Forensic Accounting
Overview
- Some of the most respected companies in the world such as World Com, Enron, Anderson, Xerox, Tyco and even Halliburton in Nigeria have been indicted of some degree of financial scandals.
- In another development, employees often steal their employers’ blind. When the enemies within bilk their companies of their money, they do so via manipulation of financial records and statements with tracks fully covered or completely erased.
Our engagement in this area is focused on resolving allegations of infractions on company policies, irregularities and all other forms of financial impropriety from inception to conclusion using Forensic Techniques. We also assist organisations in developing and implementing Corporate Fraud Policy to protect the rights of Auditors or Forensic Investigators in the company and at the same time excluding the usual “Rights of Privacy” claims by perpetrators.
Main Objectives
- To evaluate potential exposures in the financial system and recommend appropriate controls to close the “fraud gaps”
- Assisting institutions to develop and install effective Fraud Policy in place
- Help in resolving allegations of Fraud from inception to conclusion
- To generate competent and accurate Forensic Report that will be tendered in any court of law should there be a need to do so.
Main tracks in this assignment include:
- Identifying Common Symptoms of Fraud and Irregularities in Books, Records, and Computer Data: Understanding the “Red-Flags”.
- Motivations for Fraud and other Commercial Dishonesty: Controlling the Deviant Behavior in the Business Place.
- Establish Sociological Causes of Fraud and other White-Collar Crime in Organisations and Agencies of Government.
- Checkmate incidents of Cheque and Protection Strategies.
- Embezzlement Schemes and Loss Prevention Strategy.
- Resolve High-Tech Fraud
- Use Interviewing Techniques in Fraud and Forensic Investigation
- Evidence gathering and Analytical Methodologies in Forensic Investigation
- Issues of Code of Conduct as a Way of Mitigating Unethical Business Practices in Organizations
- Methods and Techniques for Computer and Accounting Forensic Investigation
- Criminal Prosecution for Fraud and Financial Crimes: Arrest, Searches, Seizures, Pre-Trial Guidelines and Sentencing Procedures
